[Matt Keeter], like many of us, has a lot of network-connected devices and an oscilloscope. He decided he wanted to look into what was on the network. While most of us might reach for Wireshark, he started at the PCB level. In particular, he had — or, rather, had someone — solder an active differential probe soldered into an Ethernet switch. The scope attached is a Textronix, but it didn’t have the analyzer to read network data. However, he was able to capture 190+ MB of data and wrote a simple parser to analyze the network data pulled from the switch.
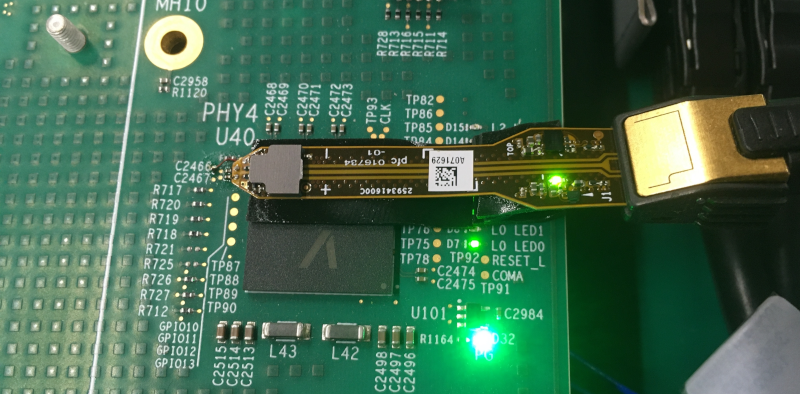
The point of probing is between a network switch and the PHY that expands one encoded channel into four physical connections using QSGMII (quad serial gigabit media-independent interface). As the name implies, this jams four SGMII channels onto one pair.
As is common in networking schemes, the 8-bit byte is encoded into a 10-bit code group to ensure enough bit transitions to recover the synchronous clock. The decoding software has to examine the stream to find framing characters and then synchronize to the transmitted clock.
What follows is a nice tour of the protocol and the Python code to decode it. It seems complex, but the code is fairly short and also executes quickly. The output? Pcap files that you can process with Wireshark. Overall, a great piece of analysis. He also points out there are other tools already available to do this kind of decoding, but what fun is that?
Wireshark can do a lot of different kinds of analysis, even if you aren’t usually capturing from a scope. You can even decrypt SSL if you know the right keys.
What’s That Scope Trace Saying? UPD and Wireshark
Source: Manila Flash Report
0 Comments